
| Vol 1, #5, April 14, 2009 |
|
April 14 , 2009 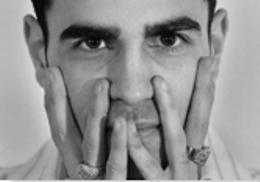  Michael Calce, aka Mafiaboy, isn't planning to hack your website...but someone just like him might be doing that right now and he wants you to be forewarned are forearmed. You may be more vulnerable than you think:
Microsoft
security report "Cybercriminals" attacking third party applications to infiltrate computers By Amy Bostock, Editor When Michael Calce, aka Mafiaboy, hacked Yahoo, CNN, E*Trade, Amazon and ebay in early 2000, his goal was to show other hackers how good he really was. Fast forward to 2009 and the motives behind computer hacking have made a dramatic shift away from bragging rights and towards becoming an organized, global criminal enterprise. The Microsoft Security Intelligence Report volume 6 released last Tuesday provides an in-depth look at how modern day cybercriminals are using software vulnerabilities (both in Microsoft and third party software) to infiltrate computers and gather data for profit. The report also offers new information on rogue security software, browser-based exploits and updates on security and privacy breaches. The Microsoft report, released twice a year, uses data gathered from hundreds of millions of computers worldwide to provide an in-depth snapshot of the threat landscape. Volume 6 covers the second half of 2008 and provides more information and insight about threats than ever before by offering new data on document file attacks and the differences in malware affecting home and business computers. When software goes bad Rogue security software, also known as “scareware”, takes advantage of the users’ desire to keep their computers safe. According to Ryan Naraine, security expert and editor of Threat Post.com, an online resource for security news, the rogue software lures users into paying for protection that is actually malware that is often designed to steal personal information The Microsoft report shows that these types of programs are now one of the top computer security threats around the world. They compromise people’s privacy and can be costly, whether by stealing banking information and draining accounts or by interfering with business productivity. “We continue to see an increase in the number of threats and complexity of those threats designed to implement crime at a variety of levels online,” says Vinny Gullotto, general manager of the Microsoft malware Protection Centre. “But as Microsoft and the industry continue to improve the security of our products and people become more concerned about their online safety and privacy, we see cybercriminals increasingly going after vulnerabilities in human nature rather than software.” How safe is your desktop? “Whether at home or at work, we are constantly passing sensitive information and that information is exposed to hackers,” says Naraine. At last week’s IT360 Conference in Toronto, he spoke about how living on an insecure Windows ecosystem is exposing users to huge risks. “Hackers today aren’t bothering to hack into operating systems,” says Naraine. “There are so many third party applications that are insecure sitting right on our desktops that they don’t have to.” Common applications like Adobe reader, Firefox and Java are commonly exploited since they, according to Naraine, are rarely patched. “Microsoft has patches built in that automatically update every month,” he says. “But when was the last time you updated your Adobe patch? This is becoming a third party nightmare for users because no one is patching.” According to the Microsoft report, nearly 90 per cent of vulnerabilities disclosed in the second half of 2008 affected applications. With friends like these… Social networking sites like Facebook are another favourite hunting ground for hackers, says Naraine. Incidences of Facebook accounts being hacked are growing rapidly, with hackers stealing and selling user names and passwords. “Social networks present great opportunities for hackers because they are more difficult to police,” he says. Take precautions Microsoft is appealing to the technology industry, law enforcement and policy makers to work together to develop new ways to deter cybercriminals and help protect user’s information online. They have offered the following tips to help individuals and businesses to be proactive in protecting their computers:
|
Contact Us For rates, opportunities, media partnerships, or to other information please contact our media sales department. {p: 905-201-6600} {t: 1-800-668-1838} Mark Henry Sales Manager, x 224 Peter O'Desse Senior Account Manager, x 223 Bill Begin, Director of Sales, 905-699-2781 Steve Lloyd, Publisher, x 225 Amy Bostock, Editor, x 221 |